Deceptive Cyber Security: Can You Spot the REAL Orion?
PUBLISHED ON Oct 03, 2012
NovaTech Automation
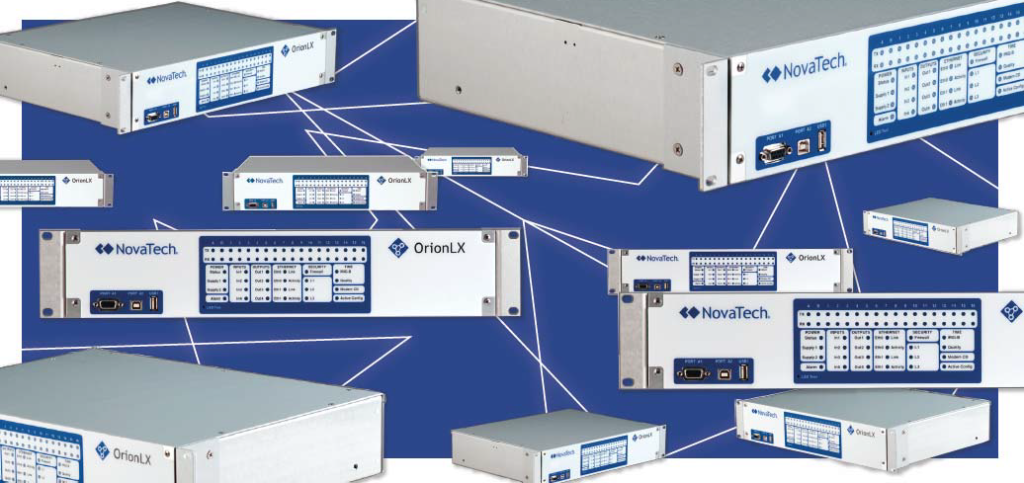
In the July 2012 issue of TechTalk we mentioned Professors Peter Idowu and Jeremy Blum of Penn State evaluating a Cyber Security approach known as a honeypot which may be applicable to the electrical utilities. In computer terminology, a honeypot is a trap set to detect, deflect, or in some manner counteract attempts at unauthorized use of information systems. Generally it consists of a computer, data, or a network site that appears to be a part of a legitimate network – and which seems to contain information or a resource of value to attackers – but is actually an isolated and monitored decoy. Professor Blum’s group emulated the encrypted communications of the OrionLX Substation Automation Platform in order to create several hundred OrionLX decoys on a test network, creating uncertainty for a potential hacker about which OrionLX is the legitimate target.
In the Penn State simulation, all traffic to the web-based applications is monitored, so that attacks specific to this device can be recorded and analyzed. In addition, the emulation system uses Snort, a popular intrusion detection system, to log and analyze attacks on other aspects of the system, for example, the web server, secure shell server, and the operating system. Given that the honeypot emulation is restricted unauthenticated access, both types of attacks would include attacks whose goals are reconnaissance of critical infrastructure or subverting or bypassing the authentication mechanism. This venture has already resulted in improvements to the OrionLX security features.
As the honeypot system is finalized, Penn State plans to work with NovaTech Automation to find a utility willing to host the honeypot system on their network. If the honeypot system is deployed in the IP address space belonging to an electric utility, it is more likely to be probed in a targeted attack and more likely to fool an attacker into believing that the honeypot is an actual device. Work is still in progress and expectations are that the system will be ready for deployment in the field later in 2012. Electric utilities interested in this next phase, please contact Ray Wright, VP Utility Marketing at ray.wright@novatechweb.com.